Table of Content
- Nist Cloud Security Danger Administration Processes
- Associated References
- Cloud Supplier Assist For Nist Csf
- H Annual Good K12 Cybersecurity Training Conference
- Pointers On Security And Privateness In Public Cloud Computing
- Nccoe Learning Collection: Cybersecurity For The Water And Wastewater Methods Sector
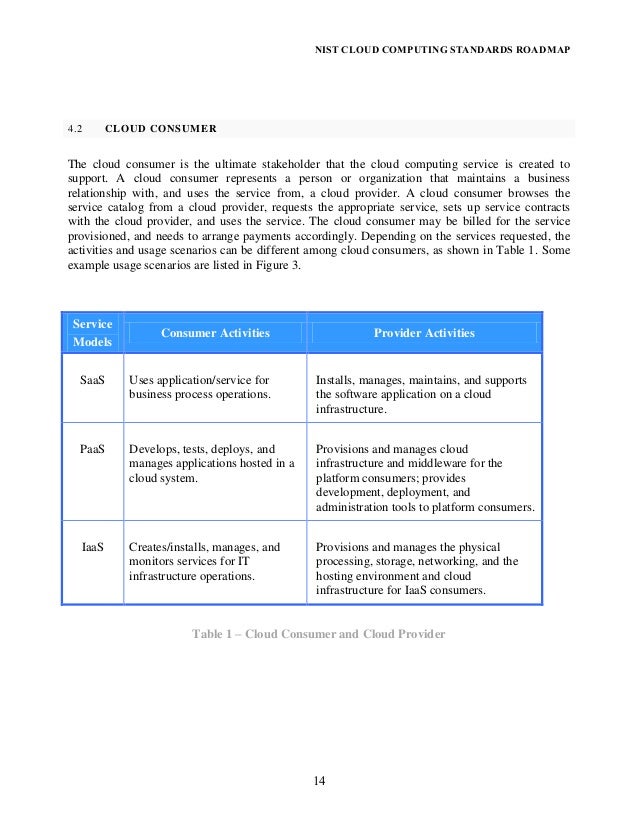
This cloud mannequin is composed of 5 important traits, three service models, and 4 deployment models. Most cloud providers combine safety and privacy controls into their cloud computing solutions, guaranteeing that these solutions meet baseline regulatory necessities. Given the multiplicity of organizations served, there is typically little to no want for cloud safety optimization. Risk administration is that you can optimize every stage in accordance with your current wants and priorities. Incorporating SDLC processes into cloud safety danger administration will also information the development of a threat management framework and streamline risk management for both cloud service providers and shoppers. To additional optimize cloud safety risk management, cloud consumers should determine which cloud service best fits their enterprise and mission-critical wants while sustaining a excessive degree of information privateness and safety.
The CSF from NIST is most helpful for small or less-regulated organizations, particularly these making an attempt to lift safety awareness. Larger organizations that have already got a centered IT security program may discover the framework less helpful. The National Institute of Standards and Technology made the Critical Security Framework so that personal organizations in the United States could make a plan for securing crucial infrastructure. It has been translated into other languages and is utilized by the governments of Japan and Israel, among different places. In its documentation, Oracle explains the NIST CSF and how its cloud products and services align with the CSF's five domains.
Nist Cloud Safety Risk Administration Processes
To obtain this, the NCCoE is collaborating with product and repair providers to provide instance implementations of trusted network-layer onboarding and capabilities that improve device and network security all through the IoT-device lifecycle. The NIST views danger administration holistically and recommends that organizations develop a set of coordinated danger management actions to effectively tackle cloud security risks. A new replace to the National Institute of Standards and Technology’s foundational cybersecurity supply chain threat management (C-SCRM) guidance aims to assist organizations protect themselves as they acquire and use expertise products and services. Some of the jobs that NIST has to do with cybersecurity are set by federal legal guidelines, govt orders, and insurance policies. For example, the Office of Management and Budget requires all federal businesses to observe NIST's cybersecurity requirements and recommendation for methods that are not part of national safety. We work onerous to involve stakeholders in setting priorities and making sure that our assets are used to handle the most important problems they face.

NIST's high priorities are cryptography, education and workforce, emerging technologies, threat management, id and entry management, measurements, privacy, reliable networks, and reliable platforms. The U.S. Department of Homeland Security Office of Inspector General is responsible for conducting and supervising independent and goal audits, inspections, and investigations of the Department of Homeland Security’s packages and operations. We work with a few of the world’s main companies, institutions, and governments to ensure the protection of their information and their compliance with applicable laws. As a cloud client, it's ultimately your duty to make certain that the cloud providers you obtain are as much as NIST security requirements and may successfully safe the privacy of your sensitive data on the cloud. Step 5 – Operationalization of cloud safety controls is authorized following the determination of acceptable operating risks to your organization’s belongings, particular person users, and different stakeholders. NIST Cloud Security Audit is a checklist of things that you have to think about when securing your corporation in the cloud.
Related References
But on the similar time, this comparatively new computing mannequin presents some unique safety concerns. After all, the flexibility to entry business-critical apps and information from anyplace and on any device also can imply it's easier for malicious actors to do the same. This web site provides video recordings of the conference program feature presentations by specialists on service mesh architecture and national leaders in DevSecOps and ZTA deployment, and demonstration of proof of idea use circumstances in multi-cloud environments. From Cloud First to Cloud Smart - The 2019 Federal Cloud Computing Strategy — Cloud Smart — is a long-term, high-level strategy to drive cloud adoption in Federal companies.
Especially in the B2B sector, achieving compliance with the NIST CSF interprets into high-value enterprise alternatives as nicely as the prospect to enter new markets. In many sectors, potential purchasers will ask outright if you are fully in compliance with the framework. How you answer that query means the distinction between whether or not you'll earn that client’s business.
Cloud Supplier Help For Nist Csf
Once the guidelines is completed, working a cloud security audit of your surroundings is very recommended. This will recheck for any kind of configuration errors, files containing sensitive and confidential information, sharing dangers, and a quantity of other different elements. Periodically run a security well being check or score audit to establish areas of improvement. Provisioning community credentials to IoT devices in an untrusted manner leaves networks susceptible to having unauthorized IoT units hook up with them. Instead, trusted, scalable, and computerized mechanisms are needed to soundly handle IoT devices all through their lifecycles, starting with secure ways to provision units with their network credentials-a course of known as trusted network-layer onboarding. For instance, inside the Detect part, AWS contains its Simple Notification Service, entry logs -- for example, from S3 -- database logs, CloudTrail, CloudWatch and other options that support detection.
It also incorporates cellphone calls, the cellular application prompts, answering safety questions, and other components. Identifying the enterprise environment that the organization works in, including its place in the provide chain and the crucial infrastructure sector. The NIST Cybersecurity Framework tells people tips on how to handle and decrease safety dangers in IT infrastructure. The CSF is made up of requirements, tips, and greatest practices that can be used to stop, detect, and reply to cyberattacks. The National Institute of Standards and Technology, or NIST, is a division of the U.S. The NIST Cybersecurity Framework assists companies of all sizes in comprehending, managing, and reducing their cybersecurity risk as nicely as safeguarding their networks and data.
H Annual Good K12 Cybersecurity Schooling Convention
Cloud suppliers have stepped up with additional documentation geared toward any ambiguities within the NIST framework. Cloud providers additionally aligned their merchandise to the NIST framework for cloud safety to help customers achieve secure cloud environments. One of the primary goals of the NIST Cybersecurity Framework is to advertise alignment between enterprise and cybersecurity. Managing threat across modern hybrid and multi-cloud environments requires a consolidated approach by which the complete risk lifecycle is considered.

AWS additionally provides risk intelligence collected from different services and then, using machine studying and AI, analyzes log knowledge. The NIST Cybersecurity Framework doesn't exist in a bubble, and it was by no means intended to work alone. In truth, it serves as the basis of many industry-specific frameworks and regulatory regimes. As such, attaining compliance takes organizations a giant step nearer in the direction of HIPAA and FISMA compliance.
Multi-cloud Security Public Working Group Mcspwg
The NIST CSF continues to be one of many security frameworks that each one U.S. industries use probably the most. The private trade and the government labored collectively to make the framework a voluntary measure. The framework was made by NIST to be versatile and cost-effective, with elements that can be put in order of significance. The NIST Cloud Security Framework is devices in a method that it's fit in addition to relevant to all businesses, regardless of industry or size. With a litany of security and compliance points exposed and in lots of cases brought on by Elon Musk’s takeover of social media platform...
Enterprises should choose between single- or multivendor SASE approaches, in addition to DIY or managed service options. AWS revealed the white paper "Aligning to the NIST Cybersecurity Framework in the AWS Cloud." It provides a short, concise breakdown of the options constructed into AWS, aligned to every of the 5 CSF domains. The doc goes area by space via each of the CSF domains -- Identify, Protect, Detect, Respond and Recover -- and correlates AWS options and capabilities to each. The Cybersecurity Enhancement Act of 2014 made NIST's work on the Cybersecurity Framework more complete.
This is the first cloud policy replace in seven years, offering a path forward for agencies emigrate to a safe and secure cloud infrastructure. This new technique will support agencies to attain extra financial savings, security, and will deliver sooner services. Cloud computing has become the core accelerator of US Government digital business transformation. NIST is establishing a Multi-Cloud Security Public Working Group to research finest practices for securing complex cloud options involving a quantity of service providers and multiple clouds. RSI Security is the nation's premier cybersecurity and compliance supplier devoted to helping organizations obtain risk-management success. RMF will assist you to negotiate safety necessities for all cloud providers you outsource.

No comments:
Post a Comment